Sponsored by Mandiant
Sponsored by Mandiant
The Forrester Wave™: Cybersecurity Incident Response Services, Q1 2022
Sponsored by Splunk
5 Automation Use Cases for Splunk SOAR
Sponsored by Lacework
Cloud Security Automation For Dummies®
Sponsored by Lacework
Les Fondamentaux de la Sécurité des Containers
Sponsored by Lacework
Transform AWS Data into Cloud Security Insights
Sponsored by Lacework
Addressing Compliance & Audit Challenges in the Cloud
Sponsored by SoSafe
The Risks of Mobile Work and How to Stay Safe
Sponsored by Elastic Security
Unifying Data Visibility for Better Threat Detection and Response
Sponsored by Palo Alto Networks
The Business Value of Prisma Cloud by Palo Alto Networks for Google Cloud
Sponsored by Elastic Security
Forrester Wave™ Endpoint Detection and Response Providers 2022
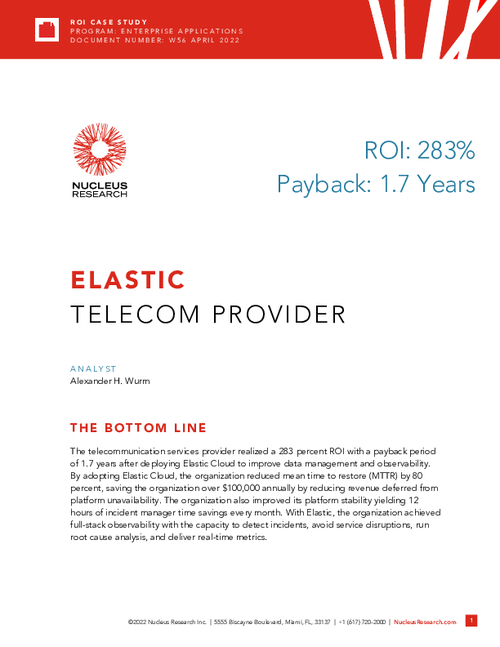
Sponsored by Elastic
Nucleus Research: Global Telecom Provider Realized 283% ROI with Elastic Cloud
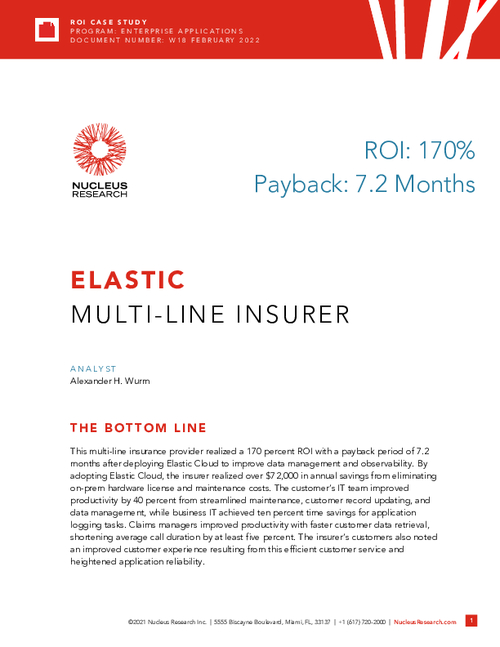
Sponsored by Elastic Security
Nucleus Research | Case Study: Realizing 170% ROI with Cloud Deployment
Sponsored by Elastic Security