Sponsored by Cyolo
Sponsored by Cyolo
Secure Digital Transformation Requires Identity-Based Access Control
Sponsored by CyberGRX
Cyber Risk Intelligence in a Digitally Transformed World
Sponsored by Mandiant
Uncover Operational Technology Threats with Data Collection
Sponsored by ServiceNow
Why Technology, Cyber, and Privacy Risk Management are Critical for Digital Transformation
Sponsored by ServiceNow
Automation Antidotes for the Top Poisons in Cybersecurity Management
Sponsored by ServiceNow
5 Ways to Weather Cybersecurity Storms
Sponsored by FICO
Application Fraud Q&A
Sponsored by FICO
Combating First-Party and Synthetic Identity Fraud
Sponsored by FICO
Application Fraud – An Open Door for Fraudsters
Sponsored by FICO
5 Strategies for Fighting First-Party and Synthetic Identity Fraud
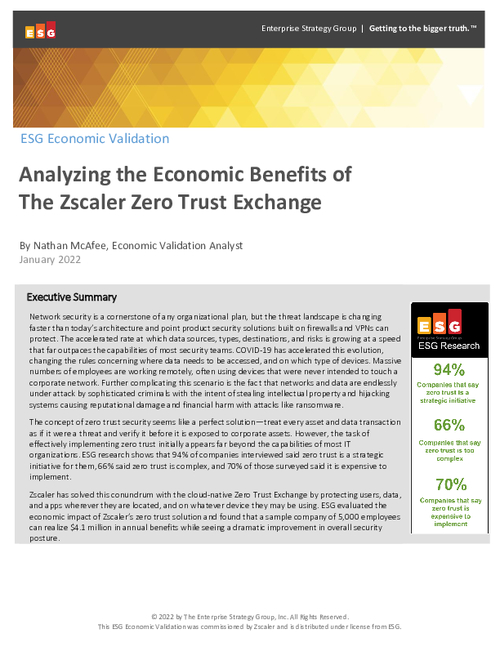
Sponsored by Zscaler