Sponsored by IBM
Sponsored by IBM
How To Cut Through The Web Of Insurance Fraud
Sponsored by Carbon Black
14 Keys to Protecting Against Ransomware
Sponsored by Level 3
Mission Critical Apps in the Cloud and New Connectivity Challenges
Sponsored by Vasco
The Changing Role of Technology within the Healthcare Sector
Sponsored by Happiest Minds
An Approach towards Integrated Cyber Security
Sponsored by Forcepoint
Superman or Superthreat? A Privileged User Risk Whitepaper
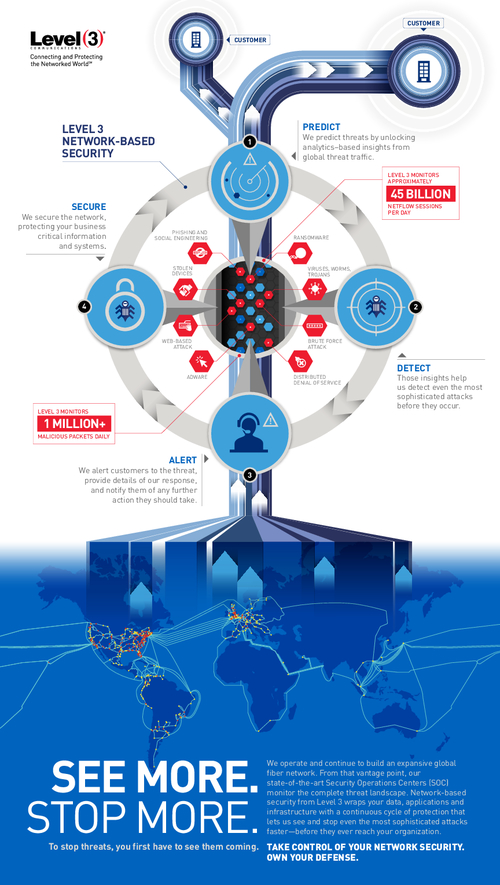
Sponsored by Level 3
Take Control of Your Network Security
Sponsored by Level 3
Global Visibility: See More to Stop More (in German)
Sponsored by Intel
Safeguarding Against Pinkslipbot
Sponsored by Intel
McAfee Labs Threats Report June 2016
Sponsored by Intel
The Benefits of Endpoint Detection and Response
Sponsored by PhishLabs
The CISO's Guide to Spear Phishing Defense
Sponsored by IBM