Sponsored by WinMagic
Sponsored by WinMagic
Enterprise Cloud Scenarios: How Intelligent Key Management Mitigates Risk
Sponsored by WinMagic
Five Things You Need To Know About Microsoft BitLocker
Sponsored by Absolute
IT Confidential: The State of Security Confidence
Sponsored by Proofpoint
How Credential Phishing is Changing and How to Stop It
Sponsored by Proofpoint
The Impostor in the Machine: Understanding the Motives and Mayhem Behind Impostor Emails
Sponsored by Proofpoint
SANS Spearphishing Survival Guide
Sponsored by Proofpoint
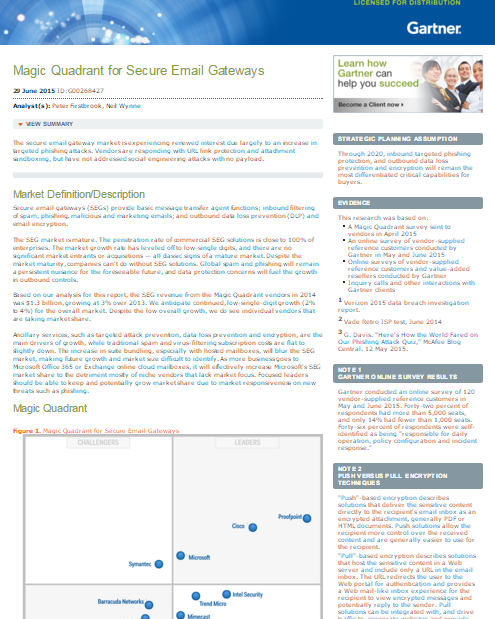
Gartner Magic Quadrant for Secure Email Gateways, 2015
Sponsored by Proofpoint
Turning the Tables on Cyber Criminals - Kill Chain eBook
Sponsored by Carbon Black
How Vulnerable is Your Endpoint Software?
Sponsored by IBM
The Case For Security Intelligence Services, Hosted From The Cloud
Sponsored by IBM
IT Executive Guide To Security Intelligence
Sponsored by IBM