Sponsored by Proofpoint
Sponsored by Proofpoint
The Impostor in the Machine: Understanding the Motives and Mayhem Behind Impostor Emails
Sponsored by Level 3
Command and Control Servers: Widespread Victimization
Sponsored by Agari
Spear Phishing is Thriving
Sponsored by Proofpoint
Critical Capabilities for Enterprise Information Archiving
Sponsored by Proofpoint
The Human Factor 2016: Advanced Threat Report
Sponsored by Proofpoint
SANS Spearphishing Survival Guide
Sponsored by Proofpoint
Gartner Magic Quadrant for Secure Email Gateways, 2015
Sponsored by Proofpoint
Enterprise Threat: The Human Factor
Sponsored by Proofpoint
Turning the Tables on Cyber Criminals - Kill Chain eBook
Sponsored by Proofpoint
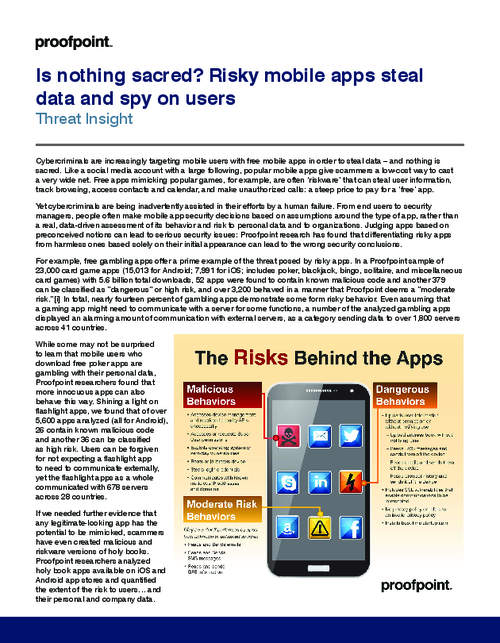
How Risky Mobile Apps Steal Data and Spy on Users
Sponsored by Proofpoint
Accelerating Office365 Adoption with Security and Compliance Controls
Sponsored by Carbon Black
How Vulnerable is Your Endpoint Software?
Sponsored by IBM
The Case For Security Intelligence Services, Hosted From The Cloud
Sponsored by IBM