Sponsored by CrowdStrike
Sponsored by Google Cloud
Google Cloud's Cybersecurity Edition: First Annual Generative AI Survey Results
Sponsored by Forta's Terranova Security
Research Results Report: Securing Your Third-Party Supply Chain Through Security Awareness
Sponsored by Google Cloud, Exabeam, Clearwater, OneTrust and Microsoft Security
First Annual Generative AI Study - Business Rewards vs. Security Risks: Research Report
Sponsored by Verimatrix
Research Survey Report: The State of Enterprise Mobile App Security
Sponsored by Palo Alto Networks
A CISO’s Guide to Attack Surface Management
Sponsored by Appgate
The 2023 Faces of Fraud Research Survey Results Report
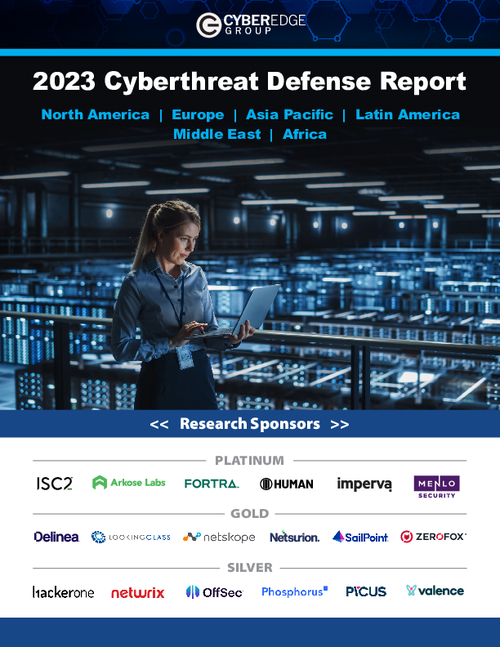
Sponsored by ISC2
The 2023 Cyberthreat Defense Report: Top 5 Insights
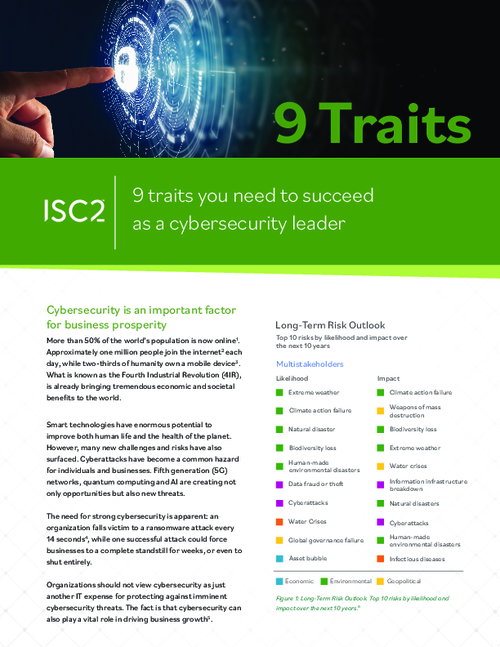
Sponsored by ISC2
9 Traits You Need to Succeed as a Cybersecurity Leader
Sponsored by ISC2
The Ultimate Guide to the CISSP
Sponsored by Palo Alto Networks
CISOs, Are You Incident Ready? | 5 Concerns for CISOs and How to Address Them
Sponsored by Proofpoint
Executive Research Report: 2023 Security Awareness Study
Sponsored by Abnormal Security