First, Last and Best Line of Defense: Perimeter Security Still Matters

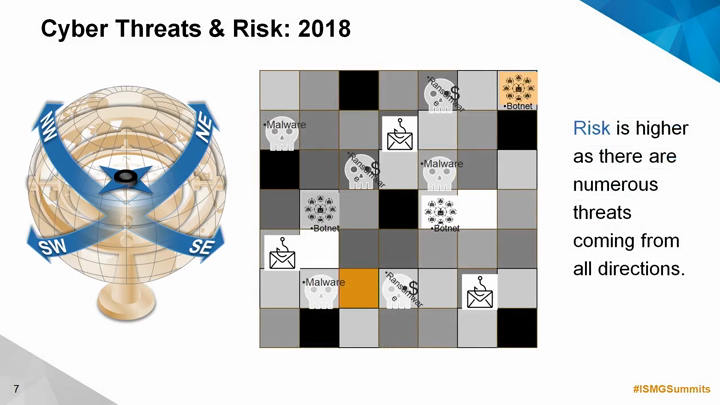
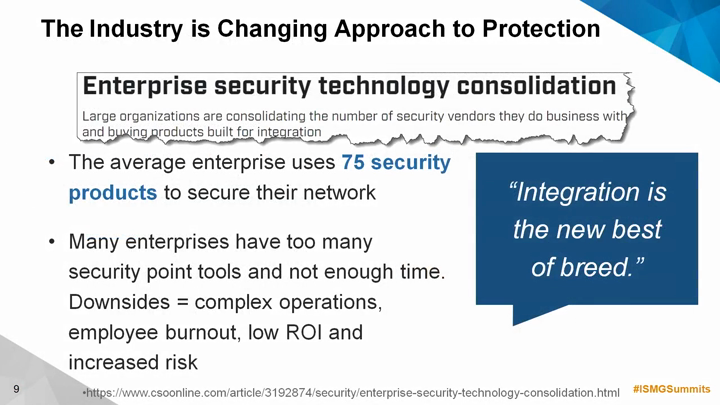
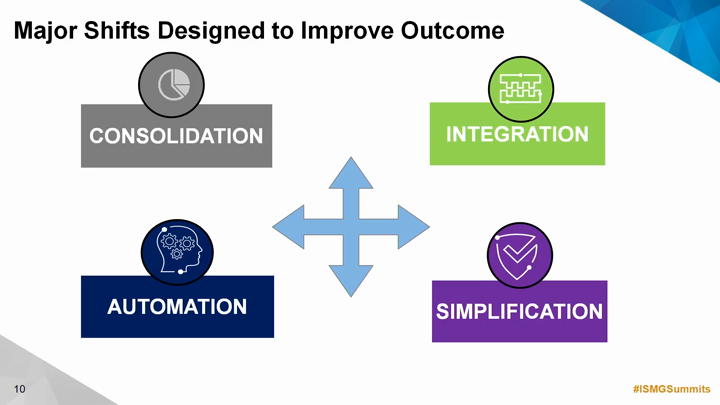
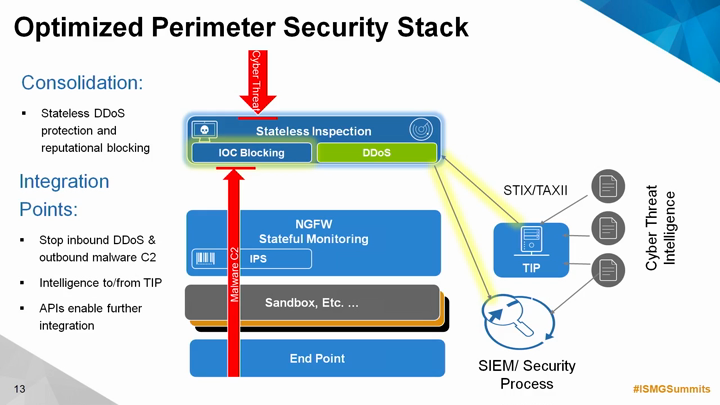
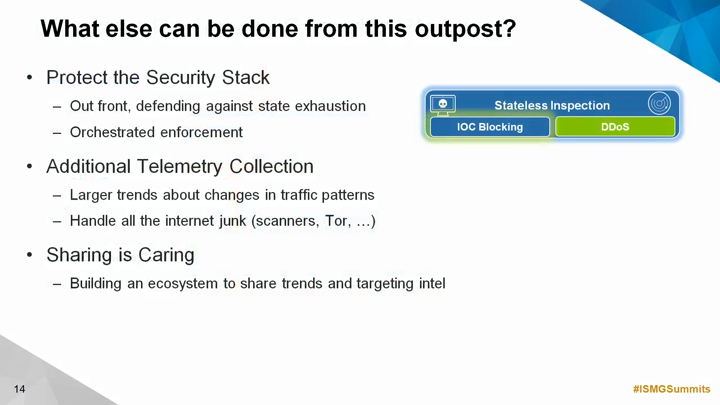
There is no shortage of security tools in any large government IT environment that are targeting specific cyber threats for a specific outcome. Yet, most agencies lack an always-on, in-line capability that allows them to operationalize their cyber threat intelligence programs. Blocking suspicious connections to internet scale threats attempting to gain access to enterprise resources is becoming the norm for security operations teams as they grapple with hiring qualified staff. Focusing on specific choke points and adding context to the threats observed and blocked enriches existing processes, we'll show how a focus on scale and correlation will make existing detection systems more effective.
Join us for an enlightening discussion on best practices around:
- Defending against internet scale threats and neutralizing the malware families that make up the global botnet threat
- Efficient blocking of malicious traffic matching Indicators of Compromise (IoCs) without tracking any session state
- Detecting and blocking outbound communication from internal compromised hosts that have been missed by other devices in the security stack
- Thwarting complex application-specific DDoS attacks and state-exhaustion techniques
- Understanding emerging threats in real-time that can be fed into other elements of the security stack via a robust set of APIs to integrate threat detection, blocking telemetry, and contextual threat intelligence into existing SOC workflows and management tools