Cybercrime , Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime
Microsoft Offers Details on Hack of Vulnerability Researchers
North Korean APT Group Apparently Involved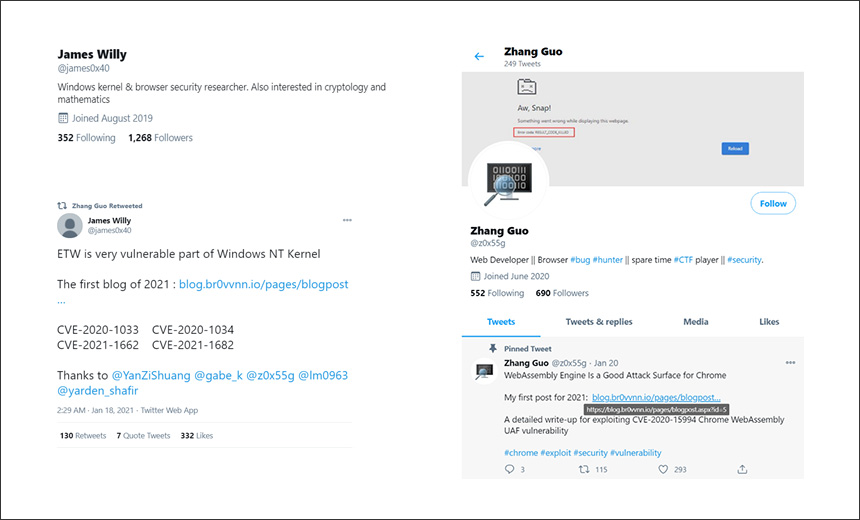
Microsoft researchers now believe that a North Korean hacking group that the company calls "Zinc" - which is better known as the Lazarus Group or Hidden Cobra - likely was responsible for targeting vulnerability researchers in an attempt to steal information via a backdoor.
This advanced persistent threat group is believed to have previously been responsible for a number of high-profile incidents, including the WannaCry ransomware attacks in 2017 (see: US Offers $5 Million Reward for N. Korea Hacker Information).
"Microsoft Threat Intelligence Center attributes this campaign with high confidence to Zinc, a [North Korea] affiliated and state-sponsored group, based on observed tradecraft, infrastructure, malware patterns and account affiliations," according to the report released Thursday.
The update from Microsoft comes a few days after Google's Threat Analysis Group reported that a North Korean government-backed group likely targeted security researchers through social media on the pretext of collaborating on vulnerability research (see: Vulnerability Researchers Hit by North Korean Hackers)
In their analysis, the Google analysts found the security researchers were targeted using a malicious Visual Basic file, which, when deployed, installed a backdoor on the victims' devices.
The Hackers
Microsoft says it started tracking the campaign by this North Korean-linked group in mid-2020. The hackers started by building a reputation in the security research community through Twitter by retweeting and posting high-quality security content and other material related to exploit research.
The hackers controlled other social media accounts and used these to amplify the other posts, Microsoft says.
After building their reputation, the hackers started approaching potential targets on Twitter and LinkedIn, according to Microsoft. "The conversations were often seemingly innocuous, asking security questions or talking about exploit techniques," the company says.
Attack Techniques
Once the hackers contacted researchers about working on a project, they shared Microsoft's Visual Studio integrated development environment tool. That tool included source code for exploiting a vulnerability, as well as an additional Dynamic Link Library file that would be executed through Visual Studio build events. The DLL would then communicate with the command-and-control server controlled by the hacking group, according to the Microsoft report. The hackers then began gathering information about the targeted victim.
"The threat actors can execute remote commands to enumerate files/directories and running processes, and to collect/upload information about the target device, including IP address, Computer Name, and NetBIOS," according to Microsoft. "Furthermore, we observed some hands-on-keyboard action to enumerate all files/directories on the target disk, create screenshots and deploy additional modules."
Microsoft also says the hackers may have exploited zero-day vulnerabilities in Windows and Chrome. They shared a blog post about vulnerability research that appears to have contained an exploit kit that deployed the zero-day attack.
"A blog post titled 'DOS2RCE: A New Technique To Exploit V8 NULL Pointer Dereference Bug' was shared by the actor on October 14, 2020, from Twitter. From October 19-21, 2020, some researchers, who hadn't been contacted or sent any files by Zinc profiles, clicked the links while using the Chrome browser, resulting in known Zinc malware on their machines soon after," according to the report.
The hackers also attempted to use other methods to infect devices. These include attempting to exploit a vulnerability in an anti-virus product, which seems to have failed because the code was buggy, the researchers say. The hackers also deployed a Chrome password stealer hosted on one of their domains.
Microsoft stresses that anyone who visited one of the hacker-controlled domains or received a file from the hackers should run a scan of their device to look for indicators of compromise and malware.
Sophisticated Campaign
Joseph Neumann, director of offensive security at consulting firm Coalfire, notes that the methods and techniques described by Microsoft show the North Korean APT group changed its approach to target the security researchers.
"Zinc threat actor’s methods in this latest campaign are not as typical as the smash and grabs we are used to seeing," Neumann says. "The approach this group used was a slow and deliberate campaign, and specifically targeted more cyber-savvy individuals who would normally not fall prey to such attacks. This sophistication is showing what adversaries are having to do to step up their game, relying more on social engineering."
Xueyin Peh, senior cyber threat intelligence analyst at security firm Digital Shadows, says that by targeting security researchers, the attackers aim to gain information on undisclosed vulnerabilities.
"Targeting the researchers in this community is undoubtedly advantageous," Peh says. "These individuals are involved in uncovering security issues and responsibly disclosing them, which often includes a trove of untapped, yet-to-be-public vulnerabilities. Gaining access to these individuals also likely provides attackers with access to privileged information, such as developments and disclosures."