Breach Notification , Governance & Risk Management , Incident & Breach Response
Developer in Cyprus Claims Breach of Contacts App
Covve Visual Network Says It's Notifying Users and Regulators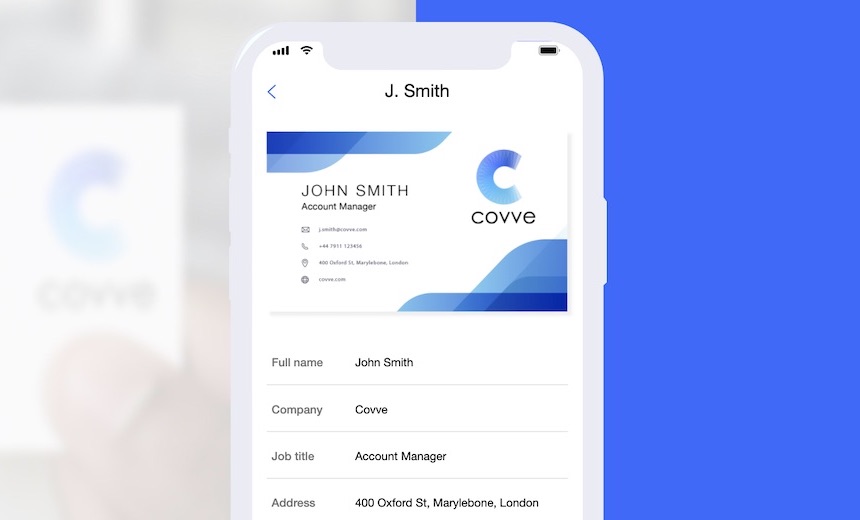
A Cyprus-based app developer acknowledges that it owns a large batch of data that apparently was left exposed on an open Elasticsearch database. A portion of the data was posted on a forum for trading data leaks.
See Also: Understanding The Implications of The Data-Breach Notification Requirement in The EU's GDPR
The developer, Covve Visual Network Ltd., said in a blog post on Saturday that it learned the day before of a possible breach of its platform.
“Our team immediately started investigating in order to determine the origin and nature of this incident,” the company writes. “User data was compromised by a third party who gained unauthorized access to one of our legacy, decommissioned systems.”
Alex Protogerellis, founder and CTO of Covve, tells Information Security Media Group that the web application that included the Elasticsearch database was decommissioned in January .
"We’re in the process of investigating this," he says.
Covve offers a contacts-storing app for iOS and Android that allows users to scan business cards, get news alerts and write notes about contacts, a CRM-like function. It sells subscriptions for more advanced features, such as daily backups.
Business Card-Like Data
The exposed data includes names, titles, email addresses, phone numbers, business names and countries. It doesn’t include financial data, birth dates or other more personal data. Also, there are no hashed passwords or passwords. The total batch is about 90 GB, encompassing tens of millions of records.
“It appears at this stage that contact data such as name and contact details was accessed, that the data cannot be associated with specific users and no user passwords were compromised,” Covve says in the blog post.
The company says in its blog post it has notified regulators; the company would be under the purview of Europe’s General Data Protection Regulation. Under GDPR, organizations can be fined up to 4 percent of their global revenue, or €22 million ($20 million), whichever is greater (see: Irish Privacy Report Gives Glimpse Into GDPR Investigations).
A portion of the data appeared in March on a well-known forum where breached data is traded. A copy of it was passed earlier this year to Troy Hunt, the Australian data breach expert who runs the Have I Been Pwned data breach notification service.
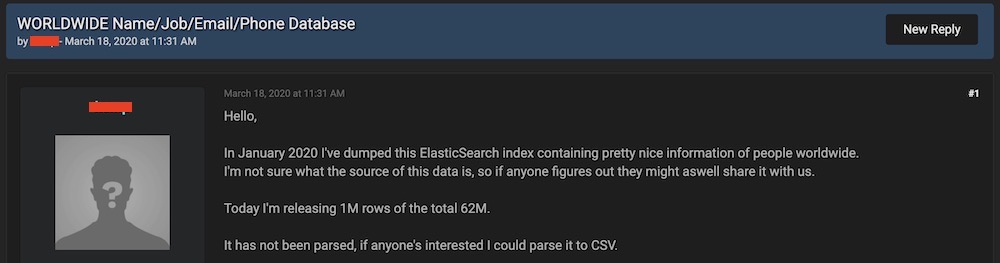
Hunt says it was a struggle to determine the owner of the data, and he blogged about those challenges. It apparently had been stored on an Elasticsearch database that that had been left open to the internet, he says.
Elasticsearch databases are often left open on the internet by mistake. Those errors have resulted in massive data breaches, including one revealed in January that exposed people’s baby photos (see: Baby's First Data Breach: App Exposes Baby Photos, Videos).
Data discovered on Elasticsearch platforms sometimes have no clear indication of where it originated. Elasticsearch clusters are often within IP ranges for big cloud service providers, which will not divulge the owner of the data.
Discovering the Owner
Hunt ended up contacting someone who he knew whose data was right besides his own in the exposed database. That person fingered Covve. Also, he took the somewhat rare action of putting the email addresses from Covve into HIPB before he knew the data came from that company.

After Hunt puts email addresses into HIPB, notifications go out to those who are registered with HIBP to be notified of new breaches. After those notifications went out, some readers of his blog had ideas of where it originated. Soon after Hunt notified Covve, the company published its own statement.
Covve is now notifying the registered users of the app. But there’s another thorny issue that is rubbing some people notified by HIBP of the breach the wrong way.
Since Covve is a contacts app, data was exposed for millions who never used Covve. Also, some of the records contained the personal notes that had been attached when a contact was inputted in Covve, which may not be information that a person would want public.
Similarly to other address book apps, CRM platforms, and mail clients, we’re not authorized under our terms to access user data," Protogerellis says. "We are getting expert advice as to how to best handle this."
Hunt says that overall, however, the data isn’t that sensitive.
“It’s minor in the scheme of things,” Hunt says. “The angle of this is more the total loss of control of our data and the fact that other people – very innocent friends – have that data and are using it in ways you didn’t expect.”