Application Security , Information Sharing , Next-Generation Technologies & Secure Development
Confide 'Confidential Messenger' Flunked Security Reviews
Flaws in App Now Fixed, But Should Serve as a Warning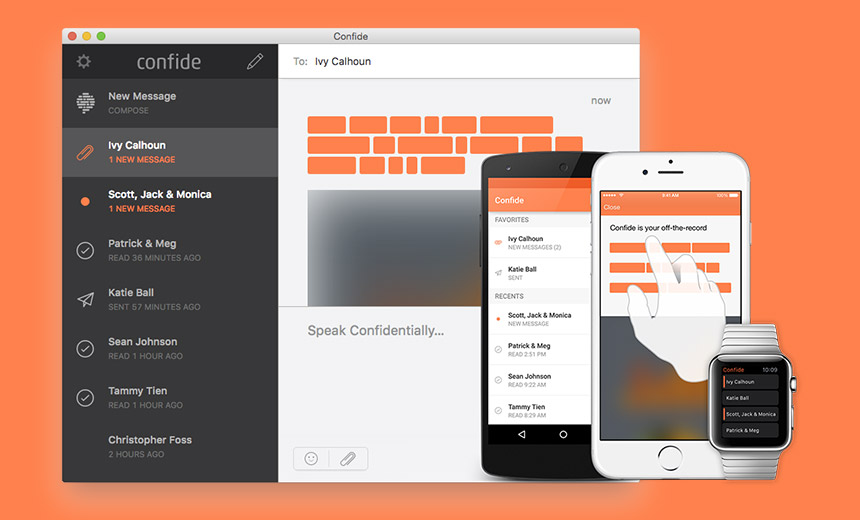
There's no dearth of supposedly secure, encrypted messaging applications - or bridges for sale in Brooklyn.
One of the latest ones - apps, that is - is called Confide, and it saw a surge in popularity after it was reportedly embraced by White House officials, including Press Secretary Sean Spicer and Director of Strategic Communications Hope Hicks, as well as to enable secret leaks documenting the inner workings of the Trump administration. Meanwhile, politicians in other countries, including Ireland, have apparently also been using it.
But all users should beware, as the application hasn't done well in two separate examinations by security companies. In fact, you might say the app flunked.
For starters, five security issues in Confide were flagged by IOActive, a Washington-based penetration testing and security company, in a March 8 report. The firm confidentially disclosed the bugs to Confide, which had fixed them by March 3.
IOActive found numerous, disconcerting problems. One could have allowed an attacker to hijack another account. Another could have allowed an attacker to pull all Confide users' contact details - including email addresses, phone numbers and real names - from the company's own database.
Meanwhile another cybersecurity firm, Quarkslab of Paris, released a technical write-up - also on March 8 - identifying some of the same issues. "The end-to-end encryption used in Confide is far from reaching the state of the art," writes Jean-Baptiste Bédrune, a security researcher with Quarkslab.
Confide officials couldn't be immediately reached for comment on the reports.
Proprietary Encryption
IOActive says it took on the research in February on its own accord, shortly after Confide received widespread press. Confide says its app uses end-to-end encryption - a scheme that leaves private keys only on end users' devices.
That's considered more secure than a centrally stored repository of keys, but only if the technology is implemented correctly. Confide also offers features seen in other, competing products, including the ability to erase text or other content after it has been viewed.
But in February, Wired reported that Confide uses a proprietary encryption protocol, which means that the code is not available for third-party experts to inspect. Security experts tend to be leery of code that they can't view, as it's impossible to determine if it has been written and implemented correctly and is free from exploitable vulnerabilities.
Confide's president, Jon Brod, did not answer questions as to whether the app underwent an independent audit, Wired reported.
Surprise, You've Been Audited
Nonetheless, Confide got audited by two different teams of security researchers anyway.
At IOActive, three researchers - Mike Davis, Ryan O'Horo and Nick Achatz - examined the desktop version of Confide for Windows and MacOS, as well as the Android app.
One of the most alarming findings concerned Confide's API, which leaked information from a backend database. Researchers recovered a sample of 7,000 user records for people who had registered with Confide over a two-day period in February.
"This data also indicated that between 800,000 and 1 million user records were potentially contained in the database," IOActive's advisory reads.
The database also leaked eight-character usernames, included an indication as to whether someone had verified their account using a link, and also included user IDs that changed in predictable increments, public encryption keys, and users' phone numbers and email addresses.
Confide also made the elementary mistake of allowing users to pick short, easy-to-guess passwords, IOActive says. It also failed to prevent brute-force attacks. Typically, web services will cut off login attempts they appear to be coming from an attacker cycling through long lists of potential passwords.
Although Confide is also designed to send encrypted messages, it could also be used to send clear-text ones, although failed to flag when this had happened. Notably, IOActive found that the app's "user interface made no indication when unencrypted messages were received."
In addition, the service was vulnerable to man-in-the-middle attacks, which would have allowed an attacker to eavesdrop on communications. "Confide failed to provide a participant [with a] fingerprint authentication mechanism, allowing Confide to conduct man-in-the-middle attacks on encrypted messages by changing the public keys sent to parties of a conversation," IOActive writes.
Picking a Messenger App
The findings are a reminder that users should be careful when selecting and relying on an allegedly secure messaging product. Encryption is superficially linked, with good reason, to better security. But developing applications and implementing encryption correctly remains complicated, and it's easy for developers to make a host of mistakes that can result in users' privacy and security being compromised.
Intelligence agencies will naturally be eager to exploit any such flaws. As we've seen in the purported CIA documents leaked this week by WikiLeaks, the agency is actively seeking alternative ways to intercept information. That includes compromising operating systems at a low level and collecting data before encryption gets applied. Such approaches appear to have helped the CIA route around encryption, and if successful would make one's choice of encrypted messaging app of little consequence(see WikiLeaks Dumps Alleged CIA Malware and Hacking Trove).
So when in doubt, and especially if your life depends on it, keep in mind that somebody could always be watching.











